The BBC’s international edition Tor version is available on the dark web, giving access to unbiased news in regions where the BBC is blocked or censored. Manual monitoring of the dark web is inefficient and risky due to the sheer volume of data involved. This early detection allows organizations to identify and respond to threats quickly, reducing the chances of unauthorized access, financial loss, or damage to brand reputation. Organizations need automated dark web monitoring to prevent cyberattacks. Since its inception, the market has catered to criminals looking for high-quality counterfeit items, such as fake IDs, passports, and branded luxury goods.
Use encrypted messaging services to communicate with sellers, and always opt for service providers that prioritize user privacy. Dark Web marketplaces, although offering a high degree of anonymity and operating beyond the reach of conventional regulatory frameworks, are fraught with scams and fraudulent activities. To keep a closer eye on your personal information, you can use services like NordStellar’s dark web monitoring. This solution scans dark web forums to alert you if your data is being listed, traded, or otherwise exposed.
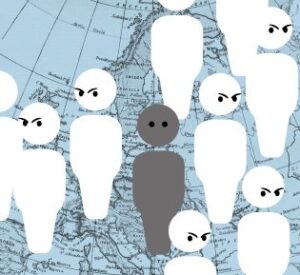
Dark Web Reveals Tech Companies Leak Most User Data

The dark web and the deep web are often used interchangeably, but they’re two distinct concepts. In short, the major difference between them is that the deep web contains internet content that you can’t find through search engines, while the dark web is a hidden network that requires a special browser to access. Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser. Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net.
A host is basically a website’s house, or where it lives and takes up space. Impreza provides an affordable hidden space for black websites to base their operations. Impreza rents servers, registers domains, and hosts email similar to sites like GoDaddy.

While this topic may seem distant for most people, understanding how these spaces operate is crucial. It helps us stay more vigilant, better protect ourselves, and make informed decisions online. It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last.
Surface Web Vs Deep Web Vs Dark Web Vs Darknet

While the percentages differ, the order of the top four languages by popularity is the same as the order for the surface web. Onion sites are prone to disappearing from the network, which will cause any attempt to reach the page to fail. This number, which provides an estimate for the size of the Tor network, complements the findings of an Onionscan report from 2017, which reported a live rate of 4,400 live sites out of 30,000.
It is a safe haven where anybody with information can share it anonymously and without fear of being tracked. The Hidden Wiki is one of the easiest ways to find useful resources and websites on the Dark Web. It is essentially a list of all the notable websites available on the Tor Network that is kept in a single, organized place.
There is no SQL code in the front-end so there is no chance of SQL injection attacks. All sensitive operationsare carried out by a completely separate process that doesn’t even know the front-end exists. I figure I’ll either see you guys this week, or after the next time someone steals all your bitcoins.
Is It Illegal To Access The Dark Web?
Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it. “This is the single most significant law enforcement disruption of the darknet to date,” U.S. Attorney Scott Brady said at a news conference Wednesday in Pittsburgh to announce the charges and the closing of the site DeepDotWeb. This case was brought in conjunction with the Joint Criminal Opioid and Darknet Enforcement (J-CODE) Team. Established within the FBI’s Hi-Tech Organized Crime Unit, J-CODE is a U.S.
The Full List Of Trusted Darknet Markets:
The defendants grew and promoted the DDW site, which functioned to drive further traffic to the DDW referral links, generating additional income for the defendants. He registered the domain, made infrastructure payments and maintained control over site content. Phan was responsible for DDW’s technical operations, designing and maintaining the website’s day-to-day operation. Phan and Prihar communicated on a daily basis to facilitate their criminal enterprise.

Dark Web Links: The Best Onion And Tor Sites In 2025
Prihar was the creator and primary administrator of the site, authorities say, while Phan led day-to-day operations. The site at various points linked to AlphaBay, Agora market, Abraxas, Wall Street Market, Tochka, Dr. D’s market, Hansa, TradeRoute, Dream Market and Valhalla. Deep Dot Web supplied 23 percent of all the users who made transactions on AlphaBay, which researchers have suggested earned an average of $600,000 and $800,000 every day until it was closed in 2017.
New York Times
The U.S. State Department helps fund the Tor project, and according to the United Nations, encryption is a fundamental human right. Facebook operates a widely used secure Dark Web portal to the social network. The Dark Web is an ominous network of shadowy hackers hellbent on stealing company data, overthrowing the country, and selling drugs to your kids with Bitcoin.
- Novices and experts alike should exercise care and caution when visiting the Dark Web.
- Many dark web search engines on the darknet suffer from spam, because these spammy sites want to be indexed and found by the search engines as opposed to genuine onion sites.
- In addition, Ahmia and Haystack make every effort to filter out and blacklist sites known to contain harmful, abusive, or illegal content.
- One of our vendors who messes around with GSM a lot is also going to post a listing for some very interesting hardware soon.
- Buyers who want to be on the escrow in the future will be able to purchase an account that has that functionality, which will be much less expensive than a vendor account.

Because Tor can be used and the Dark Web can be accessed on a traditional home PC, security professionals rely on additional security tools like the Tails operating system. Tails is a Linux distribution that can be installed on and run from a portable flash drive. By accessing the Dark Web via Tails, user behavior is never logged locally, and it is significantly more challenging for malicious software to harm the host PC. While many dark web websites, like the former black market website Silk Road, are used to facilitate criminal activity, there are also plenty of legitimate dark web websites. But anything that’s against the law on the regular web or offline is also illegal on the dark web. This includes buying or selling illicit goods, illegal transactions, and downloading copyrighted material.
“single Most Significant Law Enforcement Disruption Of The Darknet To Date”
- Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely.
- We also found that this tiny network of onion sites is tightly connected.
- Monitoring active marketplaces offers early access to malware kits, credential dumps, and fraud tools.
- By relying on encryption, pseudo-anonymous currencies, and network-level anonymity, they create a false sense of safety, drawing in both buyers and sellers.
- It also boasts that no personal information is required to use the service, and payment can be made with cryptocurrency.
SecureDrop helps whistleblowers anonymously send sensitive material to media outlets via a unique SecureDrop URL. The files are automatically encrypted, and the sender’s IP is not logged. Facebook’s onion version lets people access Facebook in countries where access to the social network is otherwise restricted. Facebook’s dark web website helps people around the world connect, communicate, and organize. So Facebook’s onion portal is a valuable tool for people living under repressive regimes.
Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them. Before your data reaches a site, Tor encrypts your connection and redirects it through a series of servers called “nodes” or “relays” to replace your IP address with each server’s address until it reaches the website.