Moreover, it’s essential to provide the company staff with enough training as well as defined objectives of...
Whether you’re a journalist, a privacy advocate, or just curious, this guide will walk you through how...
Being unprepared for or unaware of side effects – Commonly known side effects of ED medication include headaches,...
Each of these nodes removes or “peels” away a single layer, which uncovers the data’s next node...
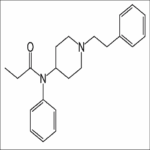
In some cases, these illicit formulations of fentanyl are made to look like other prescription opioid tablets....
From the rise of crypto-fueled markets to AI-augmented cybercrime, the numbers paint a vivid picture of a...
Jochim-Smoot recommends using Google Lens to search for images that are similar to the pieces you’re hoping...
However, some caution is warranted as the directory includes user-submitted links that may occasionally slip through without...
Whether you are trying to put an end domestic dispute or eliminate your business competitors, we have...
Another Crime Bay user in Denmark, an Italian-born woman called Emanuela Consortini, was arrested thanks to an...