
When you enter the deep web, you may feel invincible, believing that your actions can’t be linked back to you. But this false sense of security can lead to serious consequences. Law enforcement agencies have made significant strides in infiltrating these hidden networks and have successfully shut down illegal marketplaces and arrested numerous criminals. However, by most journalistic accounts, the vast majority of hitman services on the dark-web are scam sites set up to steal thousands in bitcoins from people looking to have someone murdered. By day, Chris is an IT professional, but by night he’s a dark web researcher and hacker, and wears his long hair in a ponytail.
Search Engine List – Onion Links (
- Additionally, consider using end-to-end encrypted messaging services, such as Signal or Telegram, to communicate securely with others on the Deep Web.
- Check for recent user reviews or feedback to ensure the site is still operational and legitimate.
- Wan then transferred an additional Bitcoin payment worth nearly $8,000 to the marketplace.
- To make its journalism more accessible to readers around the world, the New York Times launched its onion service in 2017.
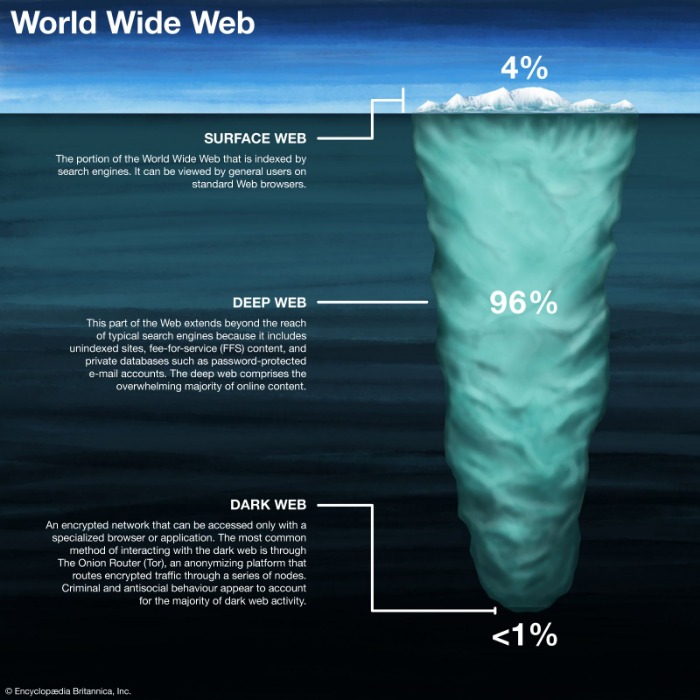
- The dark web (often referred to as the “dark net”, “black web”, or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose.
This connection can take a few moments, depending on your internet speed and network conditions. Users turn to the Hidden Wiki because it simplifies navigation through the complex and often confusing dark web. Many people seek it out for privacy and anonymity, as the Tor network and the Hidden Wiki help mask identities and activities from surveillance.
Is Using The Tor Network Illegal?
However, the dark web environment can be unpredictable and sometimes dangerous, filled with scam links, phishing sites, and other malicious threats. That is why we emphasize caution, vigilance, and adherence to best security practices when exploring these hidden corners of the internet. As when visiting ordinary websites, stay alert to security risks on onion sites.
What Services And Tools Are Available On The Dark Web?
Your real information could be exposed at these nodes, allowing third parties to intercept your dark web activity. That’s why we recommend connecting to VPN before accessing Tor—VPN encryption protects your data, and changing your IP adds an extra layer of privacy to protect you. The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, or any middleman, knowing who the other is.
Hacking Groups And Services
It publishes a newsletter in multiple languages and not only runs onion services for its website but all its email and chat services. Torch is one of the oldest and most popular onion search engines on the dark web, serving over 80,000 requests per day. Torch is funded primarily through advertising—purchased in BTC, of course—which is why you’ll find the front page blanketed with old-school banner ads of dubious origins.
These tools enable users to connect to .onion or .i2p sites that exist outside the conventional internet infrastructure. Tor, the most widely used, anonymizes traffic through layered encryption and random routing, providing a secure way to access dark web directories safely. I2P, though less popular, offers similar peer-to-peer anonymity with a focus on internal network services.
How To Find Active Onion Dark Web Sites (And Why You Might Want To)
There’s no broad consensus on dark web safety, but you at least need to use Tor and VPN together. Once you have those, there are several ways to tunnel through the dark web. Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination. A VPN hides your internet activity, making it harder for your connection requests to be traced back to you. It’s a precaution to protect yourself before diving into the dark web. For recommendations on choosing a VPN, look for expert reviews and articles.
‘Kill List’ is airing until Christmas, with fresh episodes weekly. The Tor Browser can take you to all kinds of questionable, dangerous, and potentially illegal content. That’s why knowing which dark web websites are safe to visit is vital.
What To Do If You See Something Illegal
That’s why we always recommend using a VPN over Tor—even if you feel you have nothing to hide. This just involves turning on your VPN before you open Tor and connect to dark web sites. While technically not an onion site, we’re including Sci-Hub (sci-hub.se) as an interesting example of a site you can access via Tor. Sci-Hub gives access to millions of scientific papers, mostly ones from behind paywalls. However, due to copyright infringement, Sci-Hub is considered illegal and banned in many countries. Founded around 1999 by activists in Seattle, it has since grown to over six million users worldwide.
However, we strongly advise against visiting the dark web unless you have a legitimate reason to do so. Stephen Allwine had paid Yura thousands of dollars to arrange a hit on his wife Amy. Anthonia is a fintech writer who has been involved in the crypto space since 2017 covering developments across regulations, adoption, and several other aspects of the Industry. When not neck-deep in the crypto news cycle, Anthonia spends her free time globetrotting and playing video games. The fee for the killing, said to be 10,000 euros, was to be paid from the inheritance left behind by the victim.

Many services that are allegedly offered on the dark web are scams. Some services are genuine; you can get what you want at an agreed fee. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom.

Law enforcement agencies are constantly working to track down the bad guys lurking in the shadows. Wilson said these sites took attention from the real crime being committed on the dark net, like the drug markets and the sites selling the sensitive personal information of millions of Americans. But there has still not been a killing commissioned on one of the dedicated hit-man-for-hire sites.
With advanced dark web monitoring, threat intelligence, and brand protection services, we help you uncover hidden dangers, prevent data breaches, and safeguard your reputation. Our platform ensures that your brand stays one step ahead of cybercriminals, giving you peace of mind in an increasingly complex digital landscape. Explore how Brandefense can empower your brand to thrive securely, even in the shadow of the dark web.
Not to mention the fact that you’ll get exposed to some stuff that will definitely make you take several cold showers. Fortunately, in Hidden Wiki, every website is followed by a brief description so that the user knows what to expect. You can also take a look at the blogs & essays section if you want to find some nifty coding resources. At first glance, Tor doesn’t look that different from your regular browser – it has a search bar, lots of quick-launch icons, the peeled onion icon smack in the middle of the screen. Note that the process can take anywhere from 5 to 30 minutes depending on your machine.



