The silver lining is that VPNs work on iPhones so you can mitigate the risk by connecting to one beforehand. This, joined by incredible value and the price of around $2/mo, makes PIA very attractive. Unfortunately, it’s slower than NordVPN and ExpressVPN but overall, its performance is admirable in practice. We’ve clarified how to go on the dark web anonymously with the help of a VPN.
- Your traffic is relayed and encrypted three times as it passes over the Tor network.
- RiseUp is a top dark web website that offers secure email services and a chat option.
- Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security.
- The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, or any middleman, knowing who the other is.
- All Tor Browser data is encrypted and relayed three times over the Onion Router network, which is composed of thousands of volunteer-run servers, which are known as Tor relays.
Regularly Verify And Bookmark Reliable Links

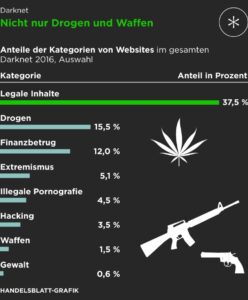
But what’s important for freedom of information in countries with strong censorship naturally also attracts many criminals. The darknet and its marketplaces not only offer drugs, medicines, doping agents, online identities, credit card data, and false passports, but also weapons of all kinds. A pivotal moment in the history of the dark web came in 2002 with the introduction of Tor (The Onion Router). Naval Research Laboratory, Tor utilized layered encryption to shield sources and destinations of internet traffic. As Tor gained traction, users flocked to it, enabling them to navigate the internet outside the boundaries of traditional scrutiny. By allowing users to hide their identities and locations, Tor laid the groundwork for the dark web as we know it today.
Recommended Verification Tools:
Accessing the Dark Web using the Tor Browser is not just about exploring hidden parts of the internet—it’s about understanding privacy and cybersecurity in the modern world. Cybersecurity Student → Conducts research on privacy tools → Accesses ethical hacking forums (legal) using Tor. Journalist in India → Uses Tor to access a whistleblowing portal → Submits information anonymously while protecting their identity. The editorial team did not participate in the creation of this guide. Gizmodo may earn a commission when you buy through links on the site. If you manage to not expose your private information and avoid illicit activities, you can be sure everything will be okay.
Use Active Monitoring Of Financial And Identity Theft
It’s, ironically, more conspicuous than using popular browsers and sites. Conversely, a site may observe a single session connecting from different exit relays, with different Internet geolocations, and assume the connection is malicious, or trigger geo-blocking. When these defense mechanisms are triggered, it can result in the site blocking access, or presenting captchas to the user. The Tor browser provides access to “.onion” websites, which are Tor hidden services that you can only access through the Tor browser. You can access these websites without worrying about someone snooping on a Tor exit node, offering more private browsing of what is known as the deep web. In 2021 a security analysis of Tor relays determined that more than a quarter of exit nodes had been compromised by a malicious actor.
Caution: Safety Comes First When Visiting Dark Web Links

So when someone like a private buyer or criminal group can’t pass the background checks or get the right permits, they usually turn to the dark web to sidestep the rules and get armed without drawing attention. The site gives out free samples of the stolen data every now and then to gain more customers. With its fast rise to fame and focus on money fraud, it’s no surprise that cybersecurity experts are keeping a very close eye on this one.
How Dangerous Is It To Click On Random Onion Links?
Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor…. It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. This includes military-grade 256-bit encryption reinforced with a 2048-bit DH key and SHA2-384 authentication to ensure your traffic arrives at its destination safely. This adds extra protection since opening Tor itself encrypts your traffic.
Too-good-to-be-true investment offers are another classic scam on the dark web. Early participants may see some profit, but that money usually comes from new victims, not actual earnings. Eventually, the system collapses, and most people lose their entire investment.
Some of these sites are very helpful (but unseen as Google doesn’t show them), while others are just for fun. Most e-commerce providers offer some kind of escrow service that keeps customer funds on hold until the product has been delivered. However, in the event of a dispute don’t expect service with a smile. Every communication is encrypted, so even the simplest transaction requires a PGP key.
How Do I Use A VPN With Tor?
Tor, or “The Onion Router” is by far the largest of these darknets. Chances are you can find it at the Imperial Library, one of the most popular sites on the dark web. But online and at your finger tips, if you can make it past the surface web. One of the most straightforward ways to access to dark web safely is via Tor, so we’ve kept that in mind when compiling our list. It scans darknet marketplaces and hacker forums to alert you instantly if anything shows up.
Risks And Essential Tips For Safe Browsing On The Dark Web
These sites aren’t accessible via standard web browsers or search engines. However, there’s a chance you may run into illegal activity on all but the best onion sites. Most internet users want to use the dark web safely, but it’s still important to be careful when using any onion browser. Originally developed to protect U.S. intelligence communications online, Tor is now used by the public for a wide range of purposes, both legal and illegal. These include bypassing government censorship, whistleblowing anonymously, conducting covert communications, and accessing or trading illicit goods and services.
How To Use Tor: Benefits And Risks Explained
It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are. The Hidden Wiki is a popular onion link directory on the dark web offering categorized lists of sites. Download the Linux version from torproject.org, extract the file, and run the start-tor-browser script. While difficult, tracking is possible if security measures are misconfigured or if users reveal personal information. Combining it with VPN and good digital hygiene improves security. Onion links are URLs that end with .onion and can only be accessed through the Tor network.
Users should also exercise extreme caution when encountering links on dark web pages. Unknown or suspicious links should be avoided as they may lead to harmful content, phishing sites, or malware. If registration is required for any service on the dark web, consider using burner accounts with no connection to your real identity. Lastly, many .onion services shut down intentionally, either temporarily or permanently. Operators might close their sites due to security concerns, legal risks, lack of funding, or shifting priorities. In some cases, they deliberately relocate to different .onion addresses to enhance security, evade detection, or maintain anonymity, leaving behind outdated and inactive links.