
And since fewer people were investing in cryptocurrency, there were fewer new accounts to hack. A recent study found that only a tiny portion of Tor’s daily users connect to the Dark Web with the intent to engage in illicit activities. This suggests that most people use Tor to surf the internet anonymously. Short for “The Onion Router,” Tor uses the decentralized onion routing network to allow users to browse the internet anonymously. Unlike VPNs, which also provide anonymity, it reroutes the users’ traffic through a network of nodes rather than just a single server. This way, Tor makes it much more difficult to trace the traffic back to the original user.
How To Protect Yourself From Identity Theft
It does not include revenues from resales along the supply chain, either further along the supply chain or as part of other products. Malware kits (“exploit kits”, US$200 to US$600) are more expensive, with which poorly skilled developers can create and distribute Malware. The so-called “zero-day iOS exploit kits” for exploiting software vulnerabilities on the day they are detected cost US$ 250,000.
Worldpay To Acquire Ravelin, A Leading AI-Native Fraud Prevention Platform
There’s also a premium account option for users who want extra benefits. And when it comes to paying, the site sticks to Bitcoin (BTC) and Monero (XMR) to keep transactions private. Understandably, as in the case with most illicit trade markets, you don’t even need to verify your email Awazon. Now, that is not to say illegal behavior is completely beyond detection. The dark web combines encryption, anonymity, and hidden doorways to provide the perfect sanctuary for such illicit activity compared to the usual internet, which is more vulnerable and trackable. We also publish VPN research and advice to help protect your internet privacy and security.
Inside A $100M Darknet Drug Empire: Taiwanese Founder Pleads Guilty
Prices range between 500 (360) and 750 for doses spurdomarket darknet market of AstraZeneca, An advert on one marketplace claiming to sell Covid-19 vaccines. The best darknet hit-for-hire idea I’ve seen is the one that uses a prediction market. Cryptocurrency is often used by cybercriminals in underground marketplaces to maintain a degree of anonymity and purchase goods and launder. Major companies operating in the dark web intelligence market are focusing their efforts on introducing intelligent and advanced solutions, such as virtual machines, to gain a competitive edge in the market. A virtual machine is a software-based copy of a physical computer that allows investigators and cybersecurity professionals to access the dark web in a secure and isolated environment.
Most Internet Users Rely On The Tor Browser To Access The Dark Web
As demand for security and customer service quality rises, Dark Web sites are adopting traditional marketing tactics such as discounts, coupons, and product reviews. The sad truth is that the growing supply of personal information on the Dark Web makes it cheaper—and therefore more likely—that your accounts will be hacked. Your data is valuable to cybercrooks, and it doesn’t cost much to steal your identity or otherwise exploit you. You might be wondering what all these (admittedly nerdy) details mean to you.
- More generally, payment services were highly prevalent, even with bank accounts and credit cards excluded.
- Fraudsters in possession of a hacked PayPal account can also try to double their money by using the account funds to run various well-established chargeback scams on merchants who accept PayPal.
- According to crypto tracing firm Chainalysis, darknet marketplaces are suffering their largest consolidation in at least five years.
- Access all our research in one place, learn about common scams and find advice on how to protect yourself from identity theft.
- This article summarizes our main findings, shares details of how hacked accounts sold on the dark web are most commonly used in fraud and shows how consumers can protect themselves from identity theft.
Darknet Dream Market Link
This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details. One thing that distinguishes BidenCash on the dark web, however, is how it markets itself. Darknet or dark web marketplaces are a hidden part of the internet that surface web users can’t access; they can only be accessed with special anonymity software called Tor.
This way, you can catch any leaks and stop them before they cause bigger problems. One of the things STYX is infamous for is having a rigorous verification process for users that makes it seem more exclusive. They even have a Telegram channel to provide their clients with live updates. Like most of the markets, STYX supports Bitcoin (BTC), Monero (XMR), and other crypto tokens to keep everyone’s identity hidden on this marketplace. The marketplace supports multiple payment methods, including Bitcoin (BTC), Litecoin (LTC), and Cryptocheck.
Cybercriminals Train AI Chatbots For Phishing, Malware Attacks
They deliberately obscure themselves from the public and can only be accessed through the Tor browser, ideally using a VPN (Virtual Private Network) for additional security. The markets are often used to buy and sell personal data, along with other contraband including weapons and illicit drugs. Simply put, if you have the cash, you can buy pretty much anything on the Dark Web. The story of Hydra is yet another in a series of creepy facts about the Dark Web. Back in 2020, this Russian-speaking marketplace was the world’s biggest darknet market. Worse yet, it was the largest marketplace for illegal drugs in all the countries of the former USSR.

Payment Platform Data
They add new batches of stolen data every other week, and there’s even a bidding system where buyers can place offers on new data batches as soon as they become available. You can even find things such as BIN checkers and PayPal cookie converters. Another reason the Russian Market is so popular is that it’s pretty inexpensive compared to other dark web marketplaces.
Any listings in currencies other than USD have been converted to USD in order to calculate average prices. The following table shows the 20 online shopping brands whose hacked account credentials were most frequently listed for sale on the darknet markets. Number of listings refers to the total number of accounts for sale, regardless of whether they are listed separately or together. The table below shows the 20 streaming services whose hacked account credentials were most frequently listed for sale on the darknet markets. The following table shows the 20 learning platforms whose hacked account credentials were most frequently listed for sale on the darknet markets.
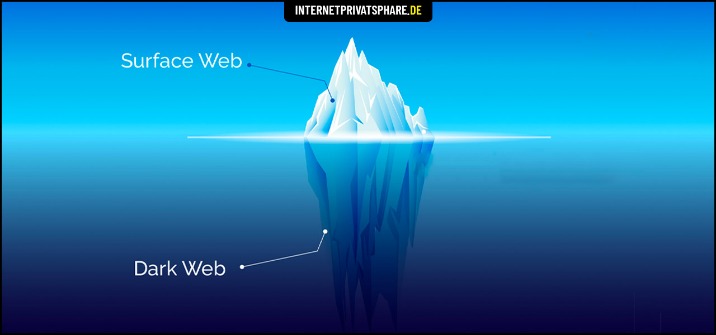
White House Market Is now one of the biggest DarkNet Markets, and the only one that only They have 5 vendor fees that is flat of finalized orders. The impact of various factors on darknet marketplace listings hopefully investigates impact of vendor reputation on price and perceived. One of the first of its kind, the Silk Road was structured as a Tor hidden service and allowed anyone with a specialized web browser to purchase. The dark web, a hidden realm of the internet accessible only through specialized browsers, has long been a hotbed for illegal activities, including the buying and selling of stolen data, hacking tools, and counterfeit goods.
Dark Web Intelligence Global Market Report 2025
More than one in five of the darknet market listings for hacked accounts that we found was for a VPN service. In response to our findings NordVPN noted that credential stuffing was a cyberattack in which credentials obtained from a data breach on one service are used to attempt to log into another, unrelated service, such as NordVPN. The company said it employed preventive measures against users of hacked account details, including rate-limiting, smart detection systems and two-factor authentication. NordVPN also said that it notified any users whose credentials were discovered to be compromised to recommend changing their passwords. There were almost three times as many NordVPN accounts than Windscribe, the next most-frequently listed VPN service. We ranked the most popular types of account (ie for streaming, VPN, payments etc) listed on the darknet markets.



