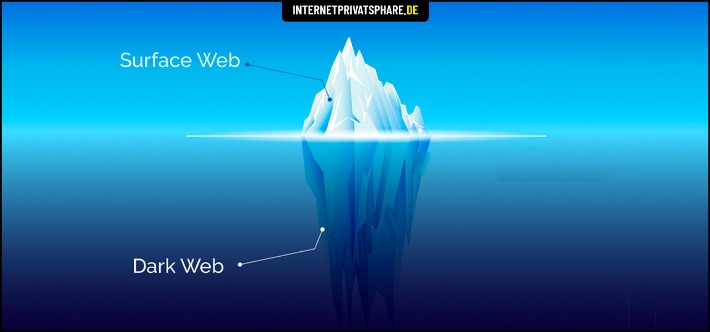
Blockchain analytics tools must evolve to include privacy coins and decentralized systems. The continued growth of dark web markets creates urgent concerns for cybersecurity professionals. Stolen data remains a top-selling commodity, with new breaches appearing almost daily. Hackers bundle login credentials, credit card details, and identity documents for sale in bulk.
Secure Drug Trade On Darknet Platforms
It routes your connection via several encryption servers to help you stay anonymous and secure. Some users want to expand and bolster their hacking skills, and hence they go to forums and look for ransomware groups. Also, you’ll find various users in the dark web message boards bragging about some of the attacks that they’ve successfully pulled off.
Alphabay Market
- These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information.
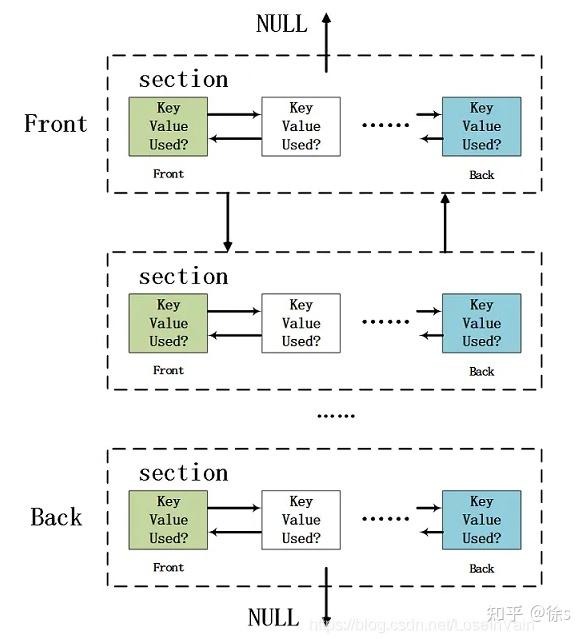
- It relies on P2P connections and requires specialized tools and software.
- Telegram channels, encrypted messaging apps, and invite-only forums support additional layers of communication and product distribution.
- That way, they can easily combat criminal and illicit activities and also help to stop data breaches and several other potential malicious attacks.
- In 2025, the darknet continues to provide a secure platform for the trade of various substances, with market lists and URLs playing a crucial role in ensuring efficient navigation.
- This transparency fosters trust and encourages vendors to maintain high standards.
Its 12,000+ users and 900+ vendors rely on a 95% trust rating, making it a go-to for quality-focused trading in the onion network. Dark web markets have exploded in scale and reach in 2025, becoming the most dangerous hubs for trading drugs, stolen data, and hacking tools. These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals.
Estimates Of Illicit Transaction Activity DO NOT Include:
The process costs a fee, but unlike other “tumbler” or “mixing” services, there is no risk that Wasabi or any of its users could scam you out of your coins. Unlike Ahmia and Haystak, however, DuckDuckGo doesn’t search .onion sites. Use it to search the normal internet from the privacy of your Tor Browser. Convert and track crypto rates for darknet marketplace transactions—stay ahead of the game. A timeline of darknet marketplace evolution, from Silk Road to 2025’s top players.
Malicious Uses Of OSINT By Cybercriminals And Hackers
Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security. The website has a sleek design and interactive user interface, making it the most preferred choice in terms of user experience. You can pay through Monera and Bitcoin using the escrow system or the traditional market account after making a purchase on this shop. You can find featured listings on the homepage and browse the products of your choice. There’s also a search bar that you can use to search for any particular product or vendor.
What Happens On Dark Web Forums?
The strategy should clearly outline how information is shared with relevant stakeholders, both internally and externally. Perhaps the strategy should include a remediation process when exploits are detected during the monitoring. The first step for any organization that wants a successful dark web forum monitoring is to start by establishing the goals, the areas to monitor, and the rules of engagement. Moreover, it’s essential to provide the company staff with enough training as well as defined objectives of what they should look for to bolster the monitoring efforts. Nevertheless, a lot of things happen in the dark web social hubs; it’s shady and illicit business most of the time, but interestingly, very active.

Infostealer Threat Actors
Many in the information security business believed the subreddit to be swarming with law enforcement agents gathering information for future arrests. AlphaBay, at its peak, hosted over 400,000 users and $600 million in yearly volume until its 2017 takedown. Despite enforcement actions, such as Hydra’s 2022 closure with $5.2 billion in seizures, markets like Abacus and Torrez persist, leveraging decentralized systems and blockchain resilience. Your definitive guide to the top darknet marketplaces of 2025—featuring verified onion routing links, cryptocurrency trading insights, vendor ratings, and escrow security details. Dive into the dark pool trading world with Abacus, Alphabay, Torrez, and more. Using a reliable VPN provider helps keep you safe when you access marketplaces on the dark web.
The combination of user-friendly interfaces, robust security measures, and diverse product offerings ensures a smooth and reliable experience for all participants. The growing popularity of darknet drug markets is driven by their ability to provide a safe and anonymous environment for trade. Users benefit from the convenience of browsing extensive product catalogs, secure communication channels, and reliable delivery systems. Tor2door Market manages 25,000+ listings and $4.5 million monthly trades via BTC and XMR, with a 7% share. Its 13,000+ users and 1,100+ vendors prioritize speed and escrow security in darknet trading. Archetyp powers 28,000+ listings and $3.5M monthly trades on BTC and XMR, securing a 6% market slice.

Ransomware Threat Actors
The use of cryptocurrencies like Bitcoin and Monero remains central to the darknet ecosystem, providing anonymity and reducing the risk of financial tracking. Additionally, the rise of decentralized marketplaces minimizes the risk of shutdowns, offering users a more stable environment for trade. These advancements will further solidify their position as a secure and reliable option for users worldwide. The rise of verified market lists has further simplified access to these platforms, ensuring users can connect to legitimate and secure marketplaces without the risk of phishing or scams. Additionally, the growing popularity of darknet forums and magazines has created a robust ecosystem where users can share reviews, discuss trends, and stay updated on new market links. In early 2025, dark web markets saw a resurgence after a relatively quiet 2024.

It’s recommended not to use new alternative links as they could just be planned exit scams. The marketplace has a pleasant, user-friendly interface built from the ground up. Its interface makes it easy to identify clone websites and ensures that users always use the authentic site. Moreover, the layers of encryption and the bounce of your data from node to node effectively mask your IP address, enabling online anonymity.
For 2025, they’re hyping a peer-to-peer escrow twist—could cut out middlemen and shake up how deals flow, which I’m stoked to see play out. It’s not as massive as Abacus, but quality’s on point—vendors deliver, and the community’s buzzing on Dread about it. I’ve poked around; it’s not overwhelming, just a tight selection that works—think curated over chaotic. If you’re into a darknet market with a community pulse and solid uptime, Bohemia Dark Market’s climbing the ranks—give it a spin if you like a vibe that’s less corporate, more crew. The forums function as secret darknet markets (most of the time) where criminals and hackers sell stolen goods. They enjoy the fact that these forums are buried in hard-to-find locations that are difficult to detect.
While accessing Darknet Markets themselves is typically not against the law in most places, engaging with illicit goods within them is generally considered a crime. On the other hand, some people might visit Darknet Markets for lawful purposes such as research, journalistic work, or simply to explore online communities. It’s essential to know the local laws regarding online activities, and be cautious when using these platforms to avoid any potential issues.
Such decentralization, along with the reuse of leaked malware source codes, will allow new, low-skilled actors to enter the ransomware ecosystem. Threat actors may also manipulate old or publicly available data to generate hype and damage reputations. Loader malware, which helps deliver harmful payloads, remained constant in supply throughout 2024. Cybercriminals innovated with multi-language programming (e.g., C++ for client components and Go for server-side panels) and offered tailored solutions to suit specific infection chains. Premium private cryptors are gaining traction, emphasizing the shift toward exclusive malware solutions. The top performers of 2025, ranked by trade volume and market influence.



