
But in the process of experimenting, I realized that the older implementation was exactly as secure as the new one, did everything I would ever need it to do, and was way simpler to use for everyone concerned. KEY TAKEAWAYS Whether you are using Android or iPhone, you can easily access the dark web on your ph… KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. KEY TAKEAWAYS If you live in a country where you don’t have internet freedom and face extreme … Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing. Also a contributor on Tripwire.com, Infosecurity Magazine, Security Boulevard, DevOps.com, and CPO Magazine.
It collects data from the public Tor network and archives historical data of the Tor ecosystem. It is an excellent option if you want to surf the web anonymously. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page.
Best Onion Sites By Category
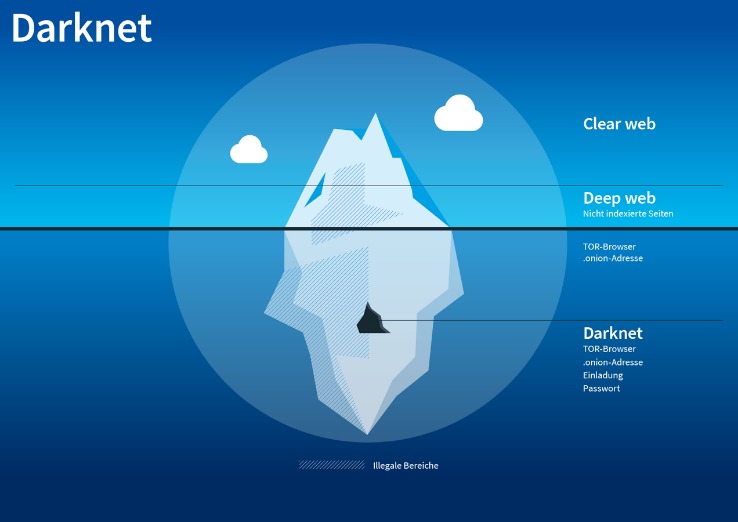
Scientific journals often put their articles behind a paywall and charge high fees for access, but Sci-Hub offers open access to read or download research papers. While it’s a deep resource, it’s also illegal in many countries, because it may violate copyright restrictions, so check out the laws in your area before visiting. The dark web is content that exists on dark nets, which require specialized software (like the Tor Browser), configurations and authorization to access. These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties.

We’re back with another video in our Webz Insider video series on everything web data. “History has taught us that this ecosystem is very, very resilient,” Christin says. “It’s part of a cycle, and we’re in the chaotic part of the cycle. We’ll have to see how it recovers. But if I were a betting person I would put more money on it recovering than on it dramatically changing.” In the digital era, the quest for sustainable revenue streams has led developers and content… The deep web offers a level of anonymity and privacy that is not possible on the surface web.

Should I Only Use A VPN To Access The Dark Web?
The more proactive you are, the better you can protect yourself against identity theft and other cyber threats. And, of course, think twice before sharing too much personal details online. Even the smallest details about you can be useful to cybercriminals. That all is for general internet activities, you can guess how crucial having a VPN is when you hop onto something like the dark web. They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk.
Never Use Your Credit And Debit Card For Purchases

Wasabi is one of the most popular cryptocurrency wallets on the dark web. Also, you can set a strong password to protect your message and choose how long it will take to expire. Unfortunately, it requires you to have an invitation code to create an account. This means you have to know someone who is already using the platform.
- It doesn’t use JavaScript, meaning the website won’t track your activities or exploit vulnerabilities.
- Before accessing any dark web site, ensure that you are using Tor or a similar service to mask your IP address.
- That’s why we always recommend using a VPN over Tor—even if you feel you have nothing to hide.
- These marketplaces are full of risks (security, legal, ethical issues – all of them).
Roundup – Best VPNs For Speed

The major issue with these websites is that a whopping 50 percent are fake, and there’s no way of telling for sure if they’ll deliver or not. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node. Though no one should bat an eye just because you’re attempting to access the dark web, keep in mind that in some countries, like the United States, even a simple foray can get you in trouble.
Key Concepts And Technologies
However long before this there was a smaller trade in illegal items dating back as much as 1970s where the students of Stanford University used the ARPANET to coordinate the purchase of cannabis. Apart from that there was also a forum called The Hive were some users dealt in Research Chemicals. One of the others most notable darknet markets was the ShadowCrew who mainly dealt in stolen credit cards but their users also traded drugs in wholesale through it’s forum. Platforms such as AlphaBay Reloaded and WhiteHouse Market have established themselves as leaders, leveraging advanced encryption and escrow systems to ensure safe transactions. These markets prioritize user anonymity, integrating features like multi-signature wallets and decentralized hosting to mitigate risks. Darknet or dark web marketplaces are a hidden part of the internet that surface web users can’t access; they can only be accessed with special anonymity software called Tor.
The Hidden Wiki
It is important to remember that the darknet market is not regulated, and there are many illegal activities that take place there. As such, there are many risks involved in accessing the darknet market, including the risk of being tracked by government agencies, hackers, and cybercriminals. According to court documents, Tal Prihar, 37, an Israeli citizen residing in Brazil, pleaded guilty to conspiracy to commit money laundering in March 2021. Beginning in October 2013, Prihar owned and operated DDW, along with co-defendant Michael Phan, 34, of Israel.
That alone might already raise suspicion and place you under special surveillance. Some reports say the FBI will simply label you a “criminal” once they’re aware you’re using the Tor browser. Then, simply click the operating system that you are using and download the file. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. It’s impossible to access the dark web with a regular browser like Chrome or Safari.
- “History has taught us that this ecosystem is very, very resilient,” Christin says.
- This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks.
- Another key player is NebulaTrade, which focuses on user anonymity through advanced Tor routing and zero-knowledge proofs.
- We recommend using NordVPN as it offers top-notch security features, including dark web threat protection.
If you’ve ever checked your medical results online through a portal that required a login, you were navigating the deep web. It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security. Vendors who can establish that they are established vendors on an existing site will be able to get a free vendor account for one week from launch.
How Do I Access Onion Sites?
And most importantly, be patient as you’ve to sort through a lot of useless results. These search engines work best if you already know what site you’re looking for, not for general browsing. Just like Google, the dark web has some search engines present on it. Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results.
The darknet has become a cornerstone for secure and efficient drug trade, offering users unparalleled privacy and reliability. By 2025, several platforms have emerged as leaders in this space, leveraging advanced encryption, decentralized systems, and user-friendly interfaces to ensure seamless transactions. Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news. That information can include checking and credit card account numbers, social security numbers, and other sensitive information.
The Department thanks the French authorities, as well as its law enforcement colleagues at the U.S. The prosecution and investigative team thanks the AlphaBay prosecution team and the Criminal Division’s Money Laundering and Asset Recovery Section for their assistance. Like ransomware, criminals can buy software and inject your devices with viruses.
The criminal groups that developed the malware gets a cut of the affiliates’ earnings, typically between 20% and 30%. IBM estimates that REvil’s profits in the past year were $81 million. Further market diversification occurred in 2015, as did further developments around escrow and decentralization. The dark web exists inside layered proxy networks, known as darknets.



