
Dark web websites are not indexed by standard search engines and can only be accessed using specialized tools, such as the Tor web browser. These sites provide a level of privacy and anonymity unavailable on the surface web, offering content and goods that cannot be easily found through traditional online platforms. The dark web may be the Wild West of the internet — a place without rules, gatekeepers, or censorship — but there are still reasons to visit. Check out our list of the best dark web links and how to navigate onion and Tor sites safely.
Navigating Ransomware Attacks While Proactively Managing Cyber Risks
DuckDuckGo is one of the leading private internet search engines on the open web. It doesn’t track your browsing history, location, or any other data. It’s so secure and privacy-oriented that the Tor browser uses it as the default search engine.
What Kind Of Content Is On The Dark Web?
You could try to visit a major site like Facebook’s onion site to check if your browser is working at all. This would verify if it’s a browser issue or just an issue with the site. Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity. That’s why we always recommend using a VPN over Tor—even if you feel you have nothing to hide. This just involves turning on your VPN before you open Tor and connect to dark web sites.
A careless misstep can lead to exposure, malware infection, or worse. To protect yourself, it’s crucial to combine multiple security layers, stay vigilant, and adopt best practices tailored for the hidden corners of the internet. Instead, they use a scrambled series of characters an average person wouldn’t have much luck memorizing.
- The aim is to reduce your online footprint as much as possible, anonymize your traffic, and disguise your location.
- In addition, know that while accessing the dark web is legal in most countries, engaging in illegal activities (buying or selling contraband, hacking services, etc.), is illegal everywhere.
- One study found that only 6.7% of Tor anonymity network daily users — a cohort that comprises mostly dark web users — connect to onion sites used for illicit activity.
- If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details.
- It’s a part of the internet that’s less regulated and more shadowy, for better and for worse.
- Onion sites may offer secure access to cryptocurrency wallets or anonymous email clients.
Remove Your Information From The Internet
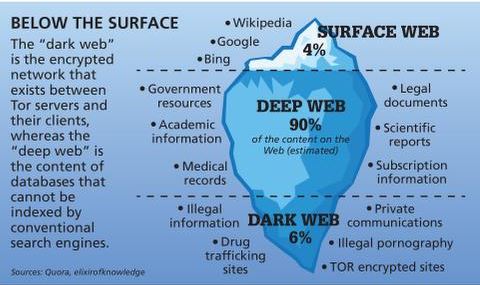
The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. For this reason, you cannot browse through these sites using your default search engine. Just like Google, the dark web has some search engines present on it.
How To Access The Dark Web Using Tor
Though people usually think of dark websites as the wrong online place, that’s not the complete truth. Although the underground internet world is rife with everything bad, it also hosts positive elements. In fact, one of its defining characteristics is constant change—onion addresses shift, platforms evolve, reputations are reassessed, and entire ecosystems rise and fall with startling speed. Navigating this fluid environment requires adaptability, ongoing vigilance, and an understanding that what works today may not be reliable tomorrow.
Verified Social Channels And News Sites
SecureDrop is an anonymous file-sharing platform designed for secure communication between whistleblowers and journalists. While anyone can use it, it’s built for high-stakes exchanges, making it overkill for routine file sharing or data backups. Major news outlets like The New York Times, The Economist, and The Guardian host SecureDrop instances on the dark web to give sources a safe, anonymous way to share sensitive information. We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal. The Tor network began as an anonymous communications channel, and it still serves a valuable purpose in helping people communicate in environments that are hostile to free speech.
Scam Links, Phishing Clones, And Honeypots On The Hidden Wiki
It’s these darknets that makes Freenet uniquely secure, as it completely blocks outside access to data shared within a darknet group. Tor Onion Services was developed to overcome the exit node problem by removing the exit node. Onion Services are websites that exist within the Tor network and can only be accessed from the Tor network. Since these websites are themselves Tor nodes, there’s no need to use an exit node that could be blocked or monitored. The extra privacy afforded by the dark web is undoubtedly abused by criminals to scam people, sell drugs, host illegal content, and more. The high-profile rise and fall of the Silk Road marketplace(new window) for illicit drugs is the best-known example of this.

I found their technical explanations clear and well-researched, though the site updates less frequently than other news platforms. TorLinks maintains one of the most reliable directories of verified .onion sites. Its strength lies in regular updates and community-driven verification of links.
- For example, you can find information unavailable to the public and share data privately while protecting your online identity.
- To use the dark web safely, use as many privacy-enhancing tools or programs as you can, and do not identify yourself in any way to anyone for any reason.
- A careless misstep can lead to exposure, malware infection, or worse.
- Following these precautions will help you explore the Hidden Wiki and the dark web with greater safety and confidence.
- We strongly recommend shielding yourself with a VPN before you access the dark web.
That’s why we took the guessing work out of it for you, and made this list of the best dark web sites you should check out. NordVPN offers a 30-day, no-risk trial subscription when you sign up on this page. This provides a full month’s access to all of the features of the #1 VPN for the Dark Web.
While accessing the dark web isn’t necessarily wrong or illegal, it’s important to know how to navigate this part of the internet safely. Accessing the dark web isn’t like surfing the web everywhere else online. Since you cannot access a library of dark web links using the regular Internet, you can check out platforms dedicated to indexing these sites, like The Hidden Wiki. This browser is the most suitable option for accessing the dark web, thanks to its multiple layers of encryption. Each time you connect to a dark web link, your request and traffic are routed through at least three different server points, ensuring your IP remains hidden. However, note that Dark.fail monitors site uptime status and cannot tell whether the site is safe.
Additionally, SentinelOne can identify sensitive data and assets within your organization, leveraging its AI-powered threat intelligence to prevent potential data breaches. You can apply automated actions to control and secure access to sensitive data. Anything beyond that index, which is hidden behind a password or any software, is known as Deep Web or Dark Web.
You will learn about dark web browsers, search engines, and other tools enabling hidden activities, and we will help you to understand the dark web legalities that may arise. The online world is much more than the websites that we regularly use in our day-to-day lives. Hidden from everyday browsing beneath social networks and corporate websites are a number of sites, markets, and forums that make up what is known as the Dark Web. According to the data, in 2023, there were over 2.5 million daily users in this hidden part of the web.
Illegal marketplaces are merely a small fraction of what’s actually there. To counter takedowns, developers are turning to decentralized DNS systems like Handshake and InterPlanetary File System (IPFS). These tools remove reliance on central registrars and servers, allowing dark web sites to persist across mirror nodes even after a seizure. While adoption is early, the shift signals a long‑term move toward censorship‑resistant infrastructure. The looming threat of quantum computing has sparked adoption of post‑quantum cryptography in anonymity networks. The Tor Project began experimenting with hybrid algorithms in 2024, and I2P is exploring lattice‑based schemes for secure routing.



