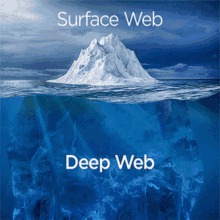
The dark web is a hidden part of the web that is not indexed by traditional search engines like Google and requires specialized software to access. In case you’re wondering how to access the deep web, chances are you already use it daily. The term “deep web” refers to all web pages that that are unidentifiable by search engines. Deep web sites may be concealed behind passwords or other security walls, while others simply tell search engines to not “crawl” them. Without visible links, these pages are more hidden for various reasons.
The part which is not indexed cannot be accessed using our regular search engines. Due to limited accessibility, we are generally unaware of the relative scale of the deepweb and darkweb in comparison to the surface web. On the Deep Web, these risks primarily relate to the fact that you need to authenticate to access a private site and that these sites contain a great deal of sensitive and valuable personal data.
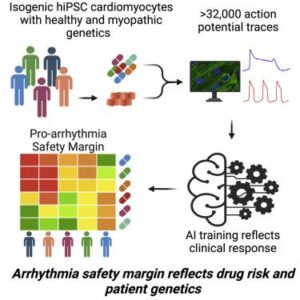
There are broadly two categories of deepweb – one is obscurity or anonymity, while the other is authenticated. There are several tools used for reaching these parts of the internet. The TOR (The Onion Router) maintains the most popular tool for Dark Web access. Law enforcement routinely shuts down and prosecutes sites and people doing illegal things on the Dark Web. The Dark Web is a small part of the Deep Web, accessible only through specialized tools like Tor (The Onion Router).
Remove Your Information From The Internet
The term dark web first appeared in print in a 2009 newspaper article describing these criminal applications. The deep web is the part of the web that can’t be reached through typical search engines and often requires getting through additional layers of encryption to access. The dark web goes a step further, providing even more layers of encryption to grant users complete anonymity.
Would you be able to tell if a cybercriminal changed one character to send you to a malware-infested copycat site? There are a lot of misconceptions about it, but we’ll answer that question once and for all in this guide. We’ll also discuss why it’s dangerous and why you should inform yourself about the dark web even if you don’t plan to be on it. When navigating beyond the surface web, there are a few key differences to keep in mind when venturing into the deep and dark web. Transform how you manage cyber risk with the CRPM platform that unifies risk across your entire organization. Additionally, check the Block pop-up windows and Warn when websites try to install add-ons settings.
- Suppose you share your name, social security number, or any other personally identifiable information on any dark website.
- You can choose the best darknet (.onion) website that suits you and start surfing.
- So basically once you have the URLs you wish to access, and the Tor browser, you can access the dark or deep web just like any other normal website.
- Accessing the deep web doesn’t require a special browser or unique protocols.
A Quick Guide On How To Use A VPN With Tor
Browsing the dark web can expose your device to malicious software. Malware, including viruses, trojans, and ransomware, can infiltrate your system, leading to data theft, loss, or damage. Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing.
Examples Of Deep Web Content:
The dark web is far from an illicit-themed zone but rather a liberating site for journalists and activists, for instance, to converse privately in constrained freedom-of-speech environments. Thus, while the dark web carries significant risks, it also highlights complex issues related to privacy and expression in the digital landscape. It is estimated that about 96% of the internet is part of the deep web, while the surface web makes up only 4%. Use Tor browser on a separate device, enable VPN for added anonymity, disable scripts, avoid downloading files, never reveal personal information, and follow organizational security policies. This solution enables security teams to identify and remediate potential threats at the reconnaissance phase, significantly reducing breach risk.
Is It Illegal To Access The Dark Web?
For instance, the search engines won’t be able to access the servers and websites hosting data about some government-led secret alien mission. A private network, tagged as the deep web, can be right next to your house. It’s just the internet that isn’t within reach of standard search engine crawlers. For instance, the network maintained by some paid streaming service. Obviously, the search engines won’t be opting for a monthly subscription to index the catalog of such websites. “The Dark Web” is an overused term that can be a source of mystery and confusion for most cybersecurity professionals.
Why Do People Use The Dark Web?
Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Some users also share links on encrypted apps like Telegram or Keybase that you can check. RiseUp is a top dark web website that offers secure email services and a chat option. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. The platform is protected from government interference and malicious attacks to protect the user. In addition, it ensures that no record of communication is stored.
Is Accessing The Dark Web Illegal?
In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites. This is where an Onion website, like the Tor browser, comes in handy. Hence, if you participate in them, whether knowingly or unknowingly, you can end up putting criminal charges on yourself, and in some extreme cases, even imprisonment. It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web.

For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question. The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities. A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. This includes military-grade 256-bit encryption reinforced with a 2048-bit DH key and SHA2-384 authentication to ensure your traffic arrives at its destination safely.
Data gleaned from ransomware and data breaches is available on the dark web. Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data. Naval Research Laboratory mathematicians and computer scientists in the mid-1990s. The U.S. Army developed “onion routing” to protect intelligence communications online. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project.
Much of the content on the deep web would not be available at all if only the surface web existed. Private databases can be as simple as a few photos shared between friends on Dropbox. They also include financial transactions made on major sites like PayPal.
Use cryptocurrency to buy anything, and use a disposable email address for any type of communication on the dark web. Check around with other users and ask if they know anything about the new marketplace. The dark web is also a place for scammers to attract vulnerable and unwitting victims.
Is It Illegal To Access The Deep Web?
You can also run a dark web scan to see if your information has been leaked on the dark web. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks. Darknets and Dark Web sites are encrypted, peer-to-peer networks that are only accessible via certain tools. Most Dark Web users use the TOR browser, which is designed to make the Dark Web easier to navigate. The TOR browser provides improved privacy and anonymity on the public Internet and makes it possible to access .onion sites on the Dark Web.