By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited. Fresh Tools Market has become a go-to platform for cybercriminals seeking access to malicious software such as keyloggers, Remote Access Trojans (RATs), and ransomware-as-a-service. Bohemia accepts Monero and Bitcoin as payment methods and places a strong emphasis on protecting user anonymity through PGP encryption. Finding a trusted dark web marketplace can be difficult, but we offer everything users need for a safe and smooth experience. Despite these takedowns, modern illegal markets have evolved by adopting decentralized hosting structures and integrating privacy-focused cryptocurrencies such as Monero to eliminate traceability.
In panels (b, c), we show the number of all sellers and buyers per quarter, respectively. In panels (d, e), we show the median net income in USD of all sellers and buyers per quarter, respectively. In panels (f, g), we show the PDF of the total money received by each seller and the total money sent by each buyer, respectively. However, owing to the difficulty of identifying relevant transactions, most studies rely on user surveys17,18 and data scraped from DWM websites19,20,21,22,23,24. In particular, these studies are based on user reviews which carry many inaccuracies, for instance, with respect to the time and value of the transaction19, that further compound error in other measures. Moreover, data scraped from the DWMs cannot assess the U2U transactions which account for the largest fraction of the total trading volume of the ecosystem13.
Separate Your Real Life From Your Online Persona
This handy feature monitors the dark web for signs that your login details or other personal info have been leaked. They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk. According to a recent trend, the dark marketplaces faced a decline in revenue. Chainanalysis, a blockchain analysis firm, conducted research that shows that the revenue decreased from $3.1 billion (2021) to $2 billion (2024).
Dark Web Monitoring Solutions: Detecting Threats Before They Happen
Not every visitor is a criminal, but this is where most cybercrimes begin. No user names are tied to actual identities, and no moderation like one may find on Reddit. Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P. One option is to try DuckDuckGo’s .onion version, which is great for privacy. Other options include Ahmia and NotEvil, which focus on listing .onion links.
Network Structure Of Transactions
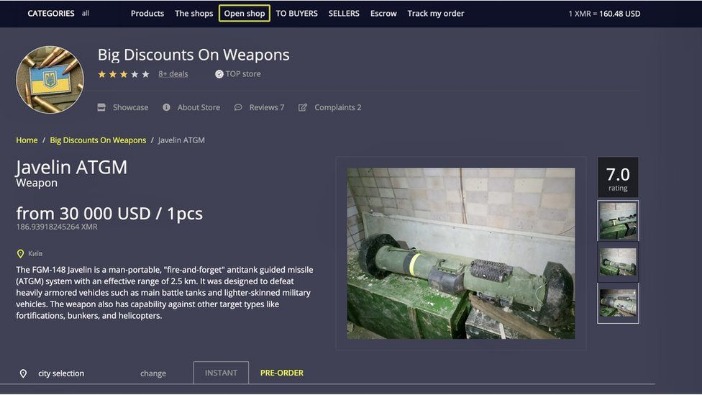
The challenges posed by these platforms are a constant reminder of the ongoing battle to the security professionals. The magnitude of illegal trade on these marketplaces is astounding, with transactions reaching millions of dollars. The lucrative nature of dark web activities fuels the growth of more such marketplaces, perpetuating the cycle of criminal behavior.
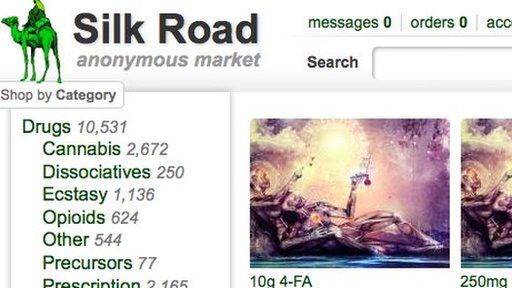
Over the next two years, the Silk Road set the standard for darknet marketplaces. By the time it was shut down in October 2013 and Ross Ulbricht arrested, the site had traded an estimated $183 million worth of goods and services. To reduce the presence of noise in the S2S network, we consider only stable U2U pairs, i.e., pairs that have at least three transactions throughout the whole period of observation13.
It includes all the essential productivity software, including MS Word and an email client. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved.
Hydra Market
This structural change is reflected in the median net income of sellers and buyers, as shown in Fig. While the curves for the seller and buyer median net income were negatively correlated before Silk Road’s shutdown, after that moment they became positively correlated. Specifically, sellers show a trend of increase and buyers a trend of decrease in their median net income before the shutdown. Our classification shows that the number of sellers is significantly smaller than the number of buyers, as shown in Figs. The number of actors in the ecosystem is affected by several factors, especially market closures. Notably, the number of buyers and sellers significantly drops after the operation Bayonet in the last quarter of 2017, which shut down AlphaBay and Hansa markets, causing a major shock in the ecosystem34.
More In Security
DWMs are accessed through darknet browsers supporting the onion routing protocol (e.g., Tor), which provides anonymous communication connections35. Additionally, transactions are made with cryptocurrencies, mostly Bitcoin, which also provide anonymity to the transaction parties6,36. While the Bitcoin blockchain is publicly available on Bitcoin core37 or other third-party APIs such as Blockchain.com38, a market or a user can generate a new address for each transaction. To track the transactions of markets and users as entities, the data need to be pre-processed in order to map groups of addresses into entities.

Users and cybersecurity professionals alike must stay informed and prepared to navigate this rapidly changing digital frontier. Overall, dark-web marketplaces inherently involve substantial risk, and users must thoroughly understand these threats. Anyone considering engaging with these platforms must carefully evaluate potential consequences, exercise stringent security practices, and remain vigilant to minimize exposure to these significant hazards. Cybercriminals on the dark web marketplace always look for new victims to target them with scams or infect their devices with malware, spyware, or adware. Thus, use the best antivirus software that protects against these online threats. Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services.
Biggest Dark Web Marketplaces
- It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor.
- With advanced dark web monitoring, threat intelligence, and brand protection services, we help you uncover hidden dangers, prevent data breaches, and safeguard your reputation.
- We showed that a small fraction of traders is responsible for a large fraction of the trading volume, and by analysing the networks of buyers and sellers, we found different resilience regimes.
- On top of that, undercover operations are a key strategy that’s being used, with agents posing as buyers or sellers to infiltrate these markets.
Much like familiar e-commerce platforms, dark web marketplaces are organized to offer a smooth buying and selling experience. However, they aren’t visible on the open internet and require specialized browsers like Tor to access. This added layer of encryption masks users’ locations, making it nearly impossible to trace activity back to individuals. Shortly after Xennt arrived in the Mosel Valley, his activities attracted the interest of a prosecutor named Jörg Angerer, who worked in the nearby city of Koblenz. Angerer, a genial and unassuming man who specializes in prosecuting cybercrime, encouraged a police investigation into CyberBunker.
In the wake of recent headlines announcing actions against Hydra Marketplace by the U.S. and German governments, darknet markets have made an ironic entrance into the spotlight. For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy. For operations security he suggests avoiding storing conversation logs, varying writing styles, avoiding mobile phone-based tracking and leaking false personal details to further obfuscate one’s identity.


Unlike many other dark web markets, Cypher does not require buyers to deposit cryptocurrency upfront, which reduces the risk of exit scams. It allows vendors to sell without registration, which provides an added layer of anonymity, making it one of the more flexible and user-friendly markets on the dark web. In this post, we’ll walk you through the top 10 dark web marketplaces that you need to watch for potential threats to your organization. When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track.
- World Market is another largest dark web shops that deals with various goods and services.
- Unlike traditional TLDs, servers using the onion TLD are more difficult to locate.
- Following Silk Road’s closure, AlphaBay emerged in 2014, introducing advanced security features such as two-factor authentication and multi-signature escrow services to improve vendor credibility.
- After a major external shock in 2017, the S2S network shrinks but, unlike the multiseller network, recovers, and grows again (though slower than the multibuyer network).
- Next up is Abacus, another newer market that has already made a massive name for itself, especially following AlphaBay’s closure.
- As security professionals continue their battle against cybercrime, Kingdom Market remains a top priority on their radar, posing significant challenges in the fight for a safer digital landscape.
Ransomware leak sites are publicity sites where ransomware groups share the details of their latest victims. However, they also play an important role in how these groups orchestrate and monetize their attacks. These sites provide the ransomware operators with a platform to accept payments from the victims, a space to shame them and apply pressure, and somewhere to leak their data if they don’t pay. Onion sites can be safe in terms of privacy protection due to strong encryption, but they also host a significant amount of illegal content and scams. It’s important to only visit trusted sites and avoid clicking on suspicious links. Navigating dark web marketplace links can be risky; however, with the right tools, you can explore safely.



