
Still, Monero was used in the majority of trades due to the anonymity it provides. Total estimated marketplace sales across its lifespan range between $300 million and $400 million, factoring in both forms of cryptocurrency. Abacus Market was launched in September 2021 under the name “Alphabet Market” but rebranded shortly afterward as Abacus.
What Is The Cost Of Stolen Data On The Darknet Market?
Looking ahead, the darknet drug trade is expected to grow further, driven by advancements in blockchain technology and increased adoption of privacy-focused cryptocurrencies like Monero. These developments will likely enhance transaction security and reduce traceability, making darknet markets even more appealing to users worldwide. Launched in September 2022, Torzon Market operates on the Tor network and features over 11,600 illegal products, including drugs and hacking tools. It enhances buyer transparency by importing vendor feedback with PGP proof. Torzon offers a premium account option for additional benefits and is valued at approximately $15 million, accepting payments in Bitcoin (BTC) and Monero (XMR).
It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. Whether you want some pharmaceutical products (drugs) or digital items, you will probably find the products here, and that too at affordable prices.
- If you ever have to connect to public Wi-Fi, make sure to use a VPN to keep your browsing safe and private.
- The typical price for these digital files was $13.97, reflecting their value when used in combination with stolen personal data to open lines of credit.
- Established in 2022, Torzon market is one of the biggest and most diverse marketplaces on the dark web.
- Meanwhile, AI-powered surveillance tools will become a staple for both attackers and defenders in this hidden economy.
- This way, you can catch any leaks and stop them before they cause bigger problems.
Legitimate Use Cases For The Average User
It allows vendors to sell without registration, which provides an added layer of anonymity, making it one of the more flexible and user-friendly markets on the dark web. Standard search engines index these websites and are accessible without special configuration. Taking the necessary precautions makes tracing your activities on the dark web difficult.
Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. Then, you can set up 2FA (two-factor authentication) for that extra touch of security in case someone somehow figures out your password. If you ever have to connect to public Wi-Fi, make sure to use a VPN to keep your browsing safe and private. According to a recent trend, the dark marketplaces faced a decline in revenue. Chainanalysis, a blockchain analysis firm, conducted research that shows that the revenue decreased from $3.1 billion (2021) to $2 billion (2024).
The 10 Biggest Dark Web Markets In 2025 – Updated List & Security Insights
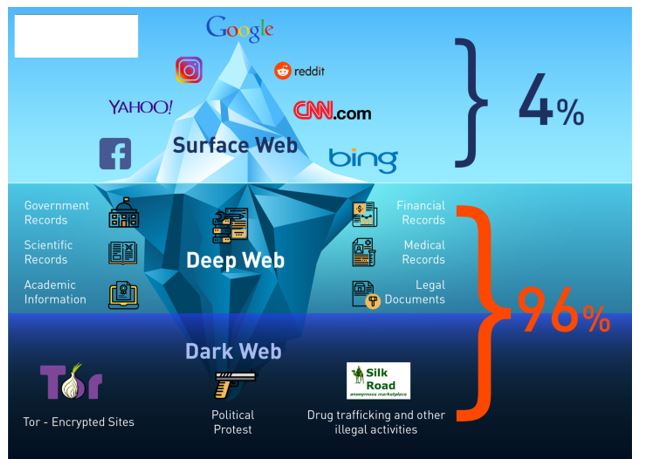
However, it’s much harder to get at the people who are doing the uploading and downloading. The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment). Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search. The dark web, which is what I’m discussing here, is a small subset of the deep web, and refers to websites that are specifically trying to stay out of sight. Parsarad is charged with conspiracy to distribute controlled substances and distribution of controlled substances in the Northern District of Ohio and elsewhere.
This browser enables access to websites with .onion domain extensions, which are specific to the Tor network. These addresses cannot be resolved by conventional DNS servers, contributing to the hidden nature of darknets. It has built a reputation for being a reliable source of stolen credit card data and PII.
Darknet Markets Explained: Navigating The Hidden Web

Based on Firefox, the Tor Browser lets you surf the clear and dark web. Ensure you download the Tor Browser from the official website to avoid downloading malware, spyware, or other viruses to your device. The easiest way to access Tor is through a special browser known as the Tor Browser. You might want to hide your Tor Browser download using a VPN and your existing browser’s private/incognito mode. Our rigorous research and testing have revealed revealing truths and busted myths.
Biggest Dark Web Marketplaces
It aims to expose abuses of power and betrayal of public trust through investigative journalism. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. Many operators have since moved to accepting only Monero (XMR),” Chainalysis added. In terms of vendor behavior, the change is largely dominated by wholesale vendors. Meanwhile, retail vendors, who operate on a smaller scale, are holding more of their illicit earnings in personal wallets, delaying conversion to fiat to avoid detection. Bitcoin’s blockchain is too leaky these days, and markets like Archetyp going Monero-only prove it.
Install The Tor Browser
Because Tor nodes are made up of volunteers, not all of them play by the rules. The final relay before your traffic goes to the destination website is known as the exit node. The exit node decrypts your traffic and thus can steal your personal information or inject malicious code. Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either.
How To Access The Dark Web: Step-by-Step Tutorial (and A Few Words Of Caution)
- With over 20 years of experience in cybersecurity and marketing, Ben has held leadership roles at companies like Check Point, Cognyte, Cylus, and Ionix.
- While hiring a hacker might sound like something out of a movie, it’s a very real threat.
- Legally, they are limited to observing publicly accessible areas using tools like the Tor browser, without engaging in unauthorized access or illegal transactions.
- Even completing a transaction is no guarantee that the goods will arrive.
- Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data.
Law enforcement takedowns, such as Archetyp, demonstrate both impact and adversary adaptation. For cybersecurity professionals, focusing on payment methods, vendor migration, and marketplace specialisation offers the most effective path to actionable intelligence. Monitoring active marketplaces offers early access to malware kits, credential dumps, and fraud tools.

Start with verified directories like Ahmia or Hidden Wiki, use a secure environment (VM + VPN + Tor), and stick to ethical, research-oriented content only. The surface web is publicly indexed, the deep web requires login or credentials, and the dark web is intentionally hidden and accessed via Tor or I2P. Use platforms like Dark.fail or Onion.live to check uptime, domain authenticity, and community trust levels before accessing a dark web site.
How Genesis Market Stole The Identity Of Over 2 Million Victims Worldwide

This means that the identities and locations of darknet users are hidden from public view and remain anonymous, even when interacting with other users or engaging in any online activity. Connecting to the Tor network might raise eyebrows depending on who and where you are. Although data sent through Tor can’t be tracked or decrypted, your internet service provider and network administrator can still see that you’re using Tor. The VPN’s encryption will hide from your ISP the fact that you’re using Tor. The dark web contains much of the internet’s illicit content, ranging from drug trafficking to child pornography sites. Tor over VPN requires you to place some trust in your VPN provider but not your ISP, and is best if you want to access .onion websites.



