Other options include Ahmia and NotEvil, which focus on listing .onion links. In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites. This is where an Onion website, like the Tor browser, comes in handy.
Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem. Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025. We developed Lunar to monitor the deep and dark web, including dark web marketplace sites. For those venturing to the shadier side of the web or those who just want to know their identity is safe, dark web monitoring tools and identity theft protection are a must-have. With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with.
The Tor Times
A VPN provides strong security for everyday browsing without the extra delays, middle checkpoint, and then finally the exit gate. The extra connection layers can act as a significant burden to your browsing experience if you’re doing something that is bandwidth intensive. This sequence offers less anonymity because your real IP address is still partially exposed along the Tor path. Plus, it’s slower since your data travels through the same four steps – entry node, relay node, exit node, and then the VPN server. Your activities on the dark web are not entirely shielded from tracking, and relying solely on anonymity can lead to a false sense of security. The dark web draws not only serious cyber criminals but also law enforcement agents aiming to catch them.
Easy Steps To Access Dark Web On Your Phone Safely In 2024
For this reason, you must watch out and avoid opening anything that looks suspicious to you. Immediately close your entire Tor Browser window (not just that active tab). Note that engaging with the content in any way is not only distressing but could also put you at legal risk. This is because law enforcement often actively monitors these sites.
On the dark web, you don’t need to be a technical expert to design ransomware, and that’s dangerous. Even people with little to no knowledge can buy ready-made ransomware and launch attacks on their victims. It’s also a marketplace for digital mercenaries; you’ll find everything from solo hackers offering their skills to well-organized groups that take on more complex or high-stakes projects.
DuckDuckGo — Private Search Engine That Can Access The Dark Web
Before clicking any of the dark web links below, you’ll need to get the Tor Browser (also called the Onion Browser) or another service that provides dark web access, such as the Brave browser. Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. Site operators can also submit their own .onion sites for indexing. George is a seasoned Cybersecurity writer who has been writing guides and news about digital security for over five years.
D Onion Websites: Between Anonymity And Risks
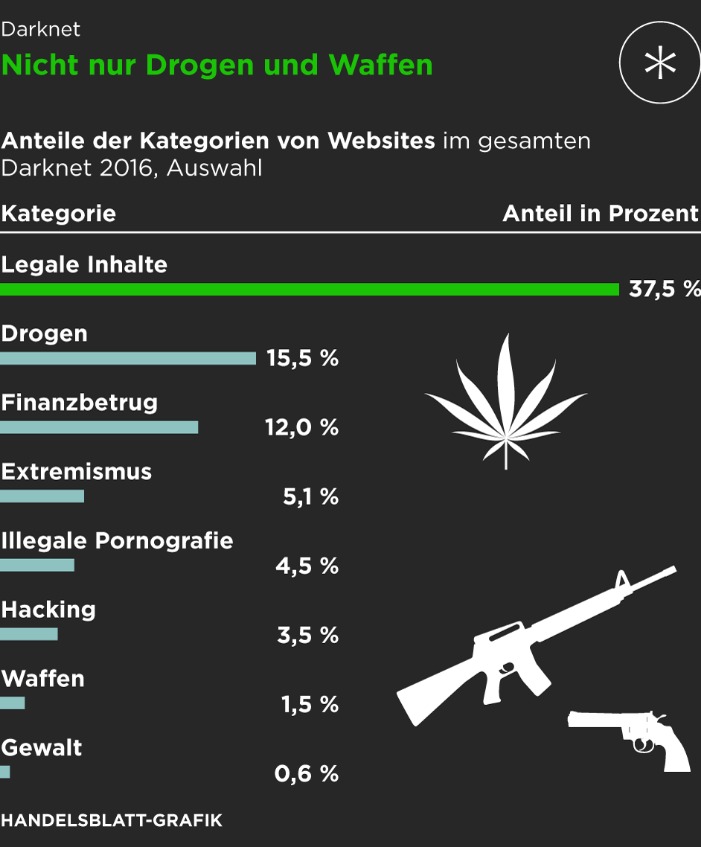
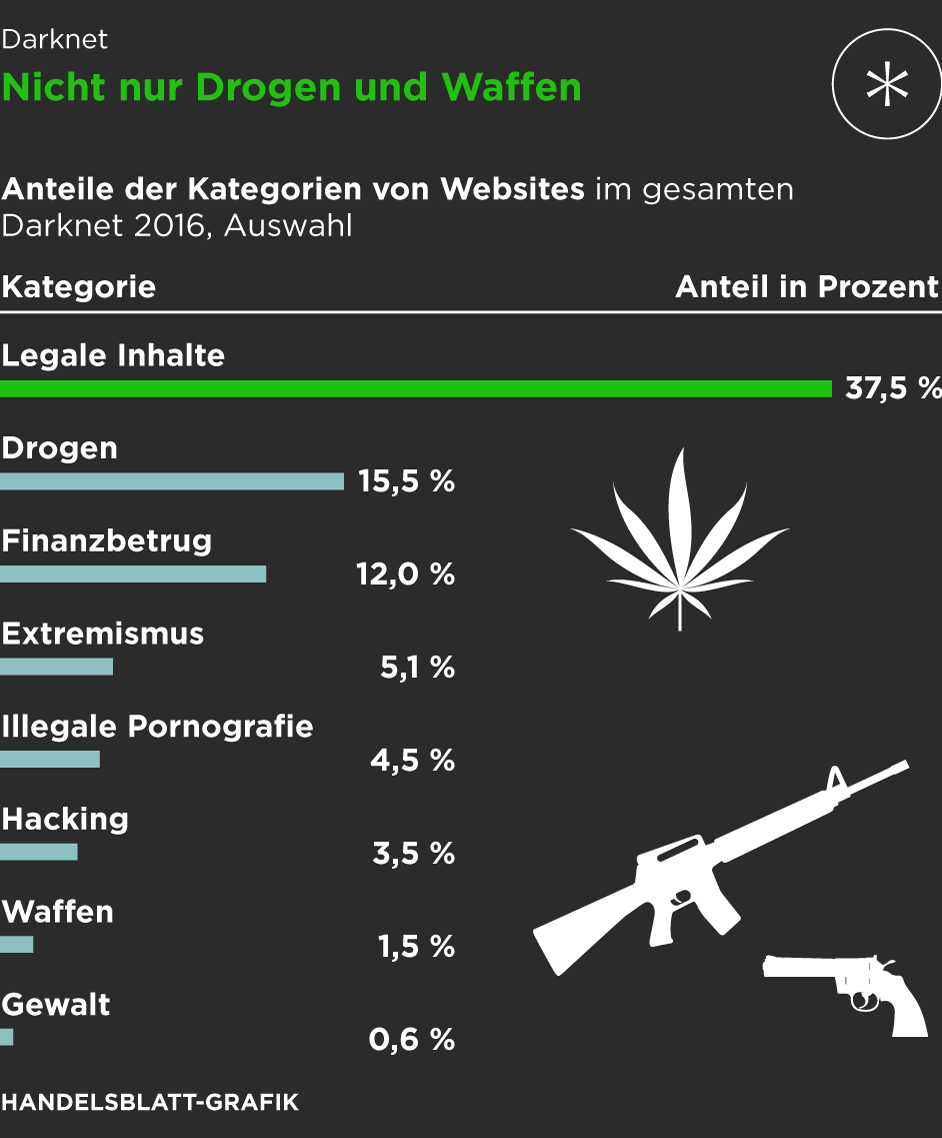
Because dark web sites can only be reached with a dark web browser like Tor browser, the best dark web sites, best onion sites, and best Tor websites are all one and the same. And because they aren’t searchable via Google or Bing, onion site lists are important roadmaps to help users find what they’re looking for on the dark web. While it may have a reputation for seedy and dangerous content, many dark web websites are legitimate and useful resources. Keep reading for a rundown of the best dark links you might want to check out. By exploring these categories of resources, users can discover that the dark web’s landscape is more nuanced than popular portrayals suggest.
MULTI-LAYERED ENCRYPTION
One of them is by using a directory of sites, like The Hidden Wiki. We strongly recommend shielding yourself with a VPN before you access the dark web. The notion that the Tor browser provides failsafe anonymity is false; you need to protect yourself. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP.
Is It Legal To Browse The Dark Web?
And thanks to ultra-secure, end-to-end encryption, your online activity is obscured. Tor Metrics is a set of tools and data provided by the Tor Project that offers insights into the performance, usage, and activity of the Tor ecosystem and its nodes. Besides monitoring and improving the network, the data can be used to detect possible censorship or attacks. Due to the privacy-forward ethos of the Tor project, Tor Metrics stresses that the data it collects must not undermine the anonymity or security of the network. The BBC and other well-known news services are blocked in some parts of the world. But people can still access independent media via BBC Tor Mirror and similar dark web news portals.

The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for. Check out these best onion sites to access the dark web securely and anonymously. Sure, it’s not as secure as the clear web version, but it’s there and totally legal to use. Hidden Facebook is hardly the only social media client on the dark web. It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers.
- The UNODC (United Nations Office on Drugs and Crime) maintains that almost all firearms are originally manufactured through legal means.
- Cryptocurrency miners and other malicious software often target dark web users.
- Facebook’s onion mirror allows people to access it in countries that block the platform, allowing people to connect across digital borders.
- AVG Secure VPN masks your IP address from other internet users, the websites you visit, and even government surveillance.
- This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks.
- DigDeeper offers in-depth analysis of technology and privacy topics rarely covered by mainstream media.
Remember, good digital habits—such as maintaining anonymity, avoiding risky behavior, and staying vigilant—form the foundation of secure dark web exploration. There are multiple search engines on the dark web that can help you find what you’re looking for. DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more.
It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown. Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2024. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement.
Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details. Therefore, for security reasons, disable JavaScript on the Tor browser and enjoy an anonymous browsing experience on the dark net. Cybercriminals on the dark web marketplace always look for new victims to target them with scams or infect their devices with malware, spyware, or adware. Thus, use the best antivirus software that protects against these online threats. The website allows visitors to view all the goods and services on display before they buy something. The quantity, price, and characteristics of the product are all provided.



