
I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged.
Popular Dark Web Links & Websites

Data like this can also help estimate how many people actively access the dark web and how many hidden websites truly exist—you can even tell where the users are accessing from. While it doesn’t index dark web content, it’s the default search engine on the Tor Browser because of its strong privacy features and lack of tracking. For searching within the dark web, specialized tools like Torch are better, as they specifically index .onion sites and hidden content. It’s simply a part of the internet that isn’t indexed by regular search engines and needs special software, like Tor, to access. However, while browsing the dark web itself is lawful, taking part in illegal activities — like buying or selling illegal goods or engaging in criminal behavior — is not.
How To Safely Access The Best Dark Web Sites – Quick Guide
However, be careful when using the Tor Browser to access the dark web. The dark web is a dangerous place, and all bets are off on your safety. This encryption and relaying of your browsing data prevents anyone who is watching from detecting which websites you are visiting.
I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges. My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world. Apparently, Hack-Rent-A-Hacker’s most popular ‘service’ is Facebook account hacking – figures! Anyway, if you’re in this sort of thing, someone can help you get inside a Facebook account for 250 euros. It goes without saying that I do not advise you to seek this sort of service. Try ZeroBin, a covert, dark web-based, communication platform that allows you to send media and text messages to your confederate.
Top 10 Dark Web Search Engines In 2025 (Tools For Staying Anonymous On The Dark Web)
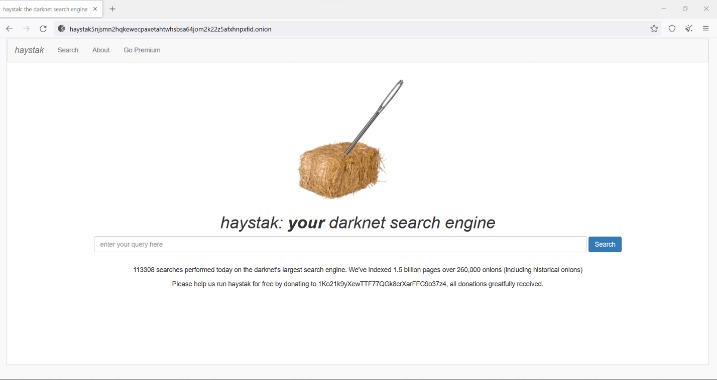
With tools like Cyble Vision, it helps organizations stay protected of cyber threats, including dark web monitoring, providing critical insights for better cybersecurity management. Haystak is a dark web browser that offers better filtering features that help users refine their search results, enabling them to locate exactly what they need. It’s one of the most well-known secret search engines on the dark web. The dark web is a mysterious place that can only be accessed with specific tools and services. To learn how to safely access the Dark Web sites listed above, read our Dark Web Access Guide here. Dark web links operate on a system of layers (like an onion) where each layer encrypts traffic as it passes through multiple relays.
Privacy Advantages Of The Hidden Wiki
- For many, it’s the first stop when venturing into the depths of the dark web.
- Also known as deep web sites, these pages typically have URLs ending in .onion and are only accessible through special software like the Tor Browser.
- But despite its many benefits, it’s sadly just a matter of fact that the dark web can be a dangerous place.
- Just like any other website, you will need to know the address of an onion service in order to connect to it.
- Freebie VPNs will track their users’ online usage, as they make money by selling this tracking info to advertisers and other nosy parties.
- Whether you’re accessing news sites or exploring the depths of Tor’s offerings, remember that knowledge and caution are your best allies.
Yes, you can access the dark web on a smartphone, but you’ll need an appropriate browser, like Tor browser for Android or Onion browser for iPhone. Remember that phones can get viruses just as easily as computers, and the chances of getting a virus likely increase when you’re browsing dark web mobile sites, no matter your platform. ProPublica is a non-profit, Pulitzer Prize-winning news outlet that focuses on abuses of power and issues of public trust.
Is Using The Tor Network Illegal?
Regular browsers can’t open Onion sites because they aren’t part of the standard domain name system. If you’re having trouble accessing a website via Tor, it could be that a node, especially the exit node, has a problem connecting to the site. We discussed how some websites block Tor traffic entirely; they do this by blocking IP addresses known to be Tor exit nodes. You can access many other sites via the Tor browser, and your requests will be routed through multiple servers to avoid monitoring. However, some websites consider Tor traffic suspicious and make users jump through several hoops, including CAPTCHAs.
How Does The Tor Browser Work?
It also connects users to hosting services and whistleblower platforms, facilitating secure communication and file sharing on the dark web. This includes password-protected sites, private databases, academic journals, and, notably, dark web services accessible only through networks like Tor or I2P. The Hidden Wiki is a gateway to these deep web resources, offering links to .onion sites that cannot be found via Google or other surface web search engines. Thus, users who want to explore hidden, uncensored, or private content often rely on tools like the Hidden Wiki because it provides structured access to resources beyond Google’s reach. It acts as a centralized hub to access sites that are not indexed by traditional search engines like Google.
A Central Directory Of onion Links

At the heart of our mission is a commitment to providing users with verified, up-to-date, and safe onion directories to help navigate the dark web responsibly. The Hidden Wiki and its alternatives offer valuable gateways to deep web content that isn’t accessible through conventional search engines. However, the dark web environment can be unpredictable and sometimes dangerous, filled with scam links, phishing sites, and other malicious threats.
A VPN masks your IP address, adding an extra layer of security and ensuring your activities remain private, even from your Internet Service Provider (ISP). This website is made public with the intention to aid the Internet users with navigation of the so called dark web. We have never received a compensation in any form for operating this website.
Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal… The deep web is not a series of sites but a storehouse of records, including email accounts, medical records, private messages, and more. We recommend installing a premium antivirus program for optimal protection against malware infections. It saves a select version of each page and preserves it even after upgrades have taken effect on the original site. Read about the adventures of modern-day explorers who have made it their mission to venture into the tunnel network of huge American universities. The site is different from our whole list, but still worth a mention.
- This means the Tor Browser is not recommended for streaming video, playing games, or downloading large files.
- So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers.
- There are several email and IM services which you can use, and it’s highly recommended to pick one if you want to step up your dark web game.
- Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely.
Another significant factor behind disappearing .onion links is action taken by law enforcement agencies. When illegal activities or content are identified, authorities may seize servers, arrest site operators, or dismantle entire networks. Consequently, previously active .onion addresses abruptly stop working, leaving users searching for new, trustworthy sources. Another critical advantage of the Hidden Wiki lies in its resistance to censorship. This makes it an essential resource for users living under oppressive regimes or in countries with strict internet controls. The Hidden Wiki empowers people to access alternative viewpoints, engage in uncensored discussions, and exercise freedom of information that surface web search engines cannot guarantee.
Failing To Verify Links
This onion site was created as a place for whistleblowers to pass information to journalists. It is a safe haven where anybody with information can share it anonymously and without fear of being tracked. The Tor network is designed to provide you with privacy and anonymity. That said, most experts agree that at least some nodes on the Tor network have been compromised by intelligence agencies like the CIA and the NSA.

FAQ: More About Onion Sites
Perhaps one of the most important features of the Tor browser is its ease-of-use – you don’t need to be a hacker in order to browse using Tor. Tor’s low barrier-to-entry allows more people to use Tor, which, in turn, helps all of its community stay anonymous in a larger sea of traffic. Sending your data along the Tor Network isn’t enough to ensure anonymity – that’s why the Tor Browser implements additional measures to safeguard your browsing. Below are a few key functionalities of the browser, and additional ones can be found in the Tor Browser’s official design document.



