In interviews, victims across the United States described in heart-wrenching detail how their lives had been upended by the abuse. Children, raped by relatives and strangers alike, being told it was normal. Adults, now years removed from their abuse, still living in fear of being recognized from photos and videos on the internet.
Tamara Ennis Was 21 At The Time Of The Shark Attack
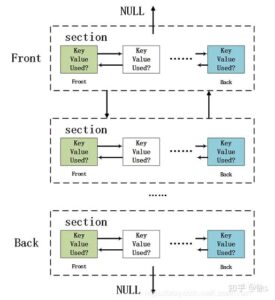
To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. In due course, the framework was remodeled and made public as a secure browser. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. The .onion site has thousands of downloadable comic books ranging from niche to mainstream.
What Are Onion Sites?
The purpose was to protect U.S. army soldiers and agents in the field, but also politicians who held secret meetings and conversations, which contained the highest security measures. Those who access the dark web do so via the Tor (The Onion Router) browser. So, that means that the number of pages increased by over 100 trillion in just over three years. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine).
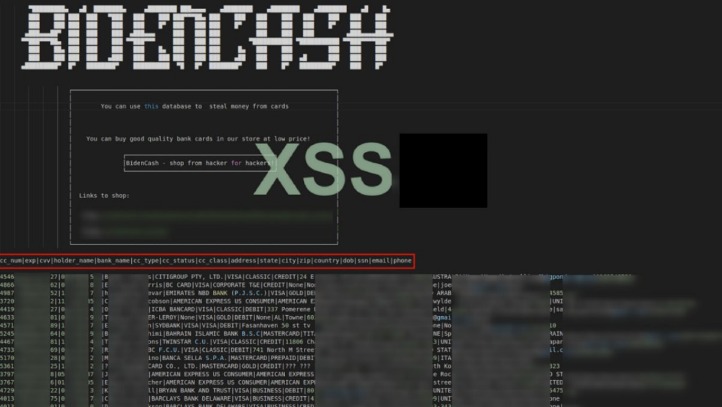
Malicious Software
Bing was said to regularly submit reports that lacked essential information, making investigations difficult, if not impossible. Snapchat, a platform especially popular with young people, is engineered to delete most of its content within a short period of time. According to law enforcement, when requests are made to the company, Snap often replies that it has no additional information. “People who traffic in child exploitation materials are on the cutting edge of technology,” said Susan Hennessey, a former lawyer at the National Security Agency who researches cybersecurity at the Brookings Institution. When reviewing tips from the national center, the Federal Bureau of Investigation has narrowed its focus to images of infants and toddlers. And about one of every 10 agents in Homeland Security’s investigative section — which deals with all kinds of threats, including terrorism — is now assigned to child sexual exploitation cases.
Related Content
That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. You risk being targeted for attacks if you explore the dark web without protection. The threat can extend to your entire network of devices connected to the internet.
The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content. The content of all these pages is stored on Google’s servers, but it’s mostly outdated, old content; smartphone app content; journals; court records; private social media profiles, and much more. JOHANNESBURG – Police say they cannot specify whether there’s an increase in crimes related to child pornography in the country.
- But as child exploitation has grown on the internet, the center has not kept up.
- Tor (The Onion Router) encrypts user traffic and routes it through a network of volunteer-operated servers, obscuring the user’s location and identity.
- Law enforcement globally has warned that a flood of AI CSAM is making it harder to identify real victims, which could complicate Europol’s task of protecting more kids through its ongoing investigation.
- When given a chance to speak, McIntosh asked the judge for hope — if not for physical freedom, he said, then for mental freedom from the “invasive, pervasive thoughts always in my mind.”
IN-CROWD OF LIKE-MINDED PEOPLE

The international investigations were led by the IRS-CI, HSI and the NCA. The Department of Justice’s Office of International Affairs of the Criminal Division provided significant assistance. Two users of the Darknet market committed suicide subsequent to the execution of search warrants.
Dallas Police Officer Arrested, Facing Family Violence Charge In Terrell
You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Some users also share links on encrypted apps like Telegram or Keybase that you can check. Another website is Dread, which is often called the “Reddit of the Dark Web.” It’s a community platform where users can discuss new markets, share onion links, add reviews, and much more.
He was linked to an account that published over one thousand posts on the site, including a post requesting child pornography, according to a news release issued by Minnesota U.S. Attorney’s Office. It uses a technology called “onion routing,” which protects users from surveillance and tracking through a random path of encrypted servers. When users access a site through Tor, their information is routed through thousands of relay points that cover the user’s tracks and make their browsing virtually impossible to trace.
Report It To The Authorities (if It’s Safe To Do So)
It’s recommended not to be too vigilant here and leave the investigation to the professionals. It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals. The use of the dark web raises suspicion as it shows there is something you want to do privately.
Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites. Then, simply click the operating system that you are using and download the file. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. It’s impossible to access the dark web with a regular browser like Chrome or Safari. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy.
You might consider investing in a VPN, or virtual private network, too, when accessing and searching the dark web. A VPN helps keeps you anonymous when searching the internet, whether you are scanning the surface web or the dark web. When using a VPN, most likely only you and your VPN provider will know what sites you have visited. While it is legal to use a VPN in the U.S., it is always the user’s responsibility to familiarize themselves with other countries’ laws before using a VPN outside the U.S.

Dark Web Child Pornography Facilitator Sentenced To 27 Years In Prison For Conspiracy To Advertise Child Pornography
Also, there’s a vast amount of unsavory content on the dark web, as well as a significantly high number of hackers and scammers looming on the platform. Check around with other users and ask if they know anything about the new marketplace. In combination with that data, and data gathered by other methods and/or tactics may in fact lead to complete exposure and could eventually lead to the police standing at your doorstep. This type of government surveillance applies mostly to countries with environments that are hostile to free speech. You can either sell or buy goods on the dark web, but both present difficulties.
- The term dark web first appeared in print in a 2009 newspaper article describing these criminal applications.
- Dubbed Operation Stream, the crackdown against Kidlfix is “one of the biggest blows against child pornography in recent years,” Guido Limmer, deputy head of the Bavarian criminal police, said while speaking to AFP.
- In a statement, the national center said it did its best to route reports to the correct jurisdiction.
- If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security.
- This Darknet website is among the first of its kind to monetize child exploitation videos using bitcoin.
- Richard Smith was prosecuted in the Eastern District of Texas and charged with transportation of child pornography.
The law Congress passed in 2008 foresaw many of today’s problems, but The Times found that the federal government had not fulfilled major aspects of the legislation. Shop for exclusive products in our marketplace, where privacy, security, and anonymity are always a top priority. Knowledge, funding, and resources for probing the marketplace are insufficient to overcome the legal and technical challenges facing investigators. ● Investigating officers must learn to identify relevant details, such as login information, that tie suspects to criminal websites. Should law enforcement implement wide-scale training, more subject matter experts are needed.