This has attracted many individuals who wish to engage in illegal activities without fear of being caught. Law enforcement has long examined online escort advertisements to identify sex trafficking victims and investigate cases. Searching online escort ads has been a common technique to proactively select cases for client (sex buyers or customers) or “john” sting operations or as part of investigating cases that began from a tip or other source.
The Full List Of Trusted Darknet Markets:
One of the oldest and most robust dark web search engines, the Torch search engine is known for being fast, straightforward, and acting as an unblocked search engine with minimal filtering. Dark web search engines are an alternative to having high technical knowledge, something hackers, journalists, and security firms are used to. With a single click of a button and going through some web pages, one can now easily visit a dark web page. It is that hidden corner of the internet that is hidden from the public and can only be used by a limited number of people. Hackers, journalists, and security companies use this hidden corner to exchange information and gather intelligence that’s not accessible through the regular internet. The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures.
The cost of being a spectator was 0.1 bitcoin; this works out to approximately $1,500 CAD. I knew what a red room was because I had just been on a surface website discussing some of the most disturbing content on the dark web. Although many of the websites have kitschy designs reminiscent of websites from the ‘90s, the level of obscurity the sites maintain is far more sophisticated.
The sentiment and affect analysis allow determining violent and radical sites that impose significant threats 11 . This here, to this child, is probably normal, and they know nothing else,” Herman said at a press conference on Thursday, motioning to the photos of the home. And we’re not going to allow it.” The child was found to be living in “horrible conditions,” Herman said. Photos released by the the Precinct 4 office showed the condition of the home, located in the 6100 block of Jadecrest Court in Spring.
OnionLand Search
Although Memex research currently revolves around the sex trade, Cafarella’s innovations can help solve other problems in science, industry, and government. Computer code and web crawlers can’t, of course, perfectly translate the human reality captured in sex ad data. As we enter 2025, these tools are adapting with improved security and functionality to meet user needs. Renowned for its precision, it offers highly accurate and relevant results, making it a trustworthy resource for dark web users. DeepSearch is an open-source search engine designed for exploring the dark web within the Tor network. It is designed to ensure user anonymity while offering access to a diverse array of information available on the dark web.
Market Features
By working together, we can help prevent the exploitation and abuse of vulnerable individuals on the dark web. Payments for sexual services on the dark web are typically made through cryptocurrencies, such as Bitcoin, which allow for anonymous transactions. This makes it difficult for law enforcement agencies to track and prosecute individuals who engage in prostitution on the dark web.
Reflections On The Intersection Of Mental Health, Human Trafficking And Unjust Criminalization

It involves the trafficking of humans for sexual exploitation, forced labour, begging, domestic servitude, child soldiers, and organ removal. Traffickers are trained to identify vulnerability factors such as poverty, unemployment, and naivety, to enable them to recruit, persuade, and manipulate victims. While traditional channels of human trafficking remain in place, cyberspace allows traffickers to exploit a greater number of victims globally and conduct other trafficking operations. The internet in particular greatly aids human traffickers in their operations with dire consequences for victims. Based on this, this paper posits that human trafficking is a dark side of cyberspace.
The last section of the chapter offers different alternatives to improve the effectiveness of response in the fight against online sexual offenses targeting minors, suggesting both predictive analysis and the importance of proactive solutions. In conclusion, prostitution on the dark web is a dangerous and illegal activity that poses significant risks to sex workers and victims of human trafficking. Combating this problem requires a multi-faceted approach that includes law enforcement, education, and awareness campaigns. By working together, we can help to prevent the exploitation and abuse of vulnerable individuals and make the internet a safer place for everyone. The trafficking of children in the EU is mostly for sexual exploitation, with the largest proportion of foreign children, mainly girls, trafficked from Nigeria.
Silk Road And Early Markets
White says he wants to expand user testing every quarter until he and his team have created a version of Memex that they are comfortable handing over to law enforcement agencies and prosecutors. When this handover happens, software components like the Web crawler, machine learning algorithms and graph analysis that can scour both the surface and deep Webs will be installed locally at law enforcement agencies. They will be connected to regular browser-based software that agencies and the general public would typically use, such as Firefox and Chrome. This would ensure that law enforcement could access the software from any Internet-connected device.
Accessibility Links
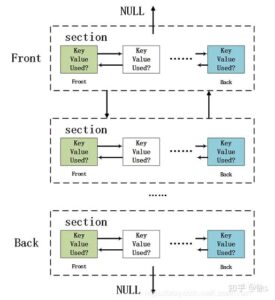
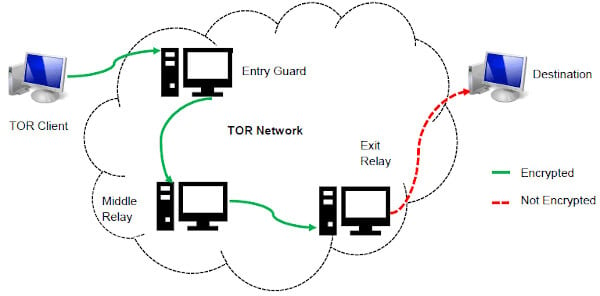
Messages are sent encrypted (using the asymmetric encryption) then they are sent through some nodes of networks known as onion routers. This technique protects the intermediate nodes form “being informed” about the source, destination and message content 1 14 16 . The technique is derived from the disciplines such as informatics, mathematics, science, statistics, social sciences, public policy, and linguistics. Different SNA techniques have developed for examining forum posting and website relationships.
Why Security Leaders Prefer To Buy CTI Solution For SaaS Platforms In 2025
This year, the Global Slavery Index 2018 report found that trafficking in human beings was higher than previously thought in European countries, with an approximate average of 3.6 million people trafficked within Europe in 2018. The dark web is a notorious corner of the internet where illegal activities thrive. One such illicit activity is the sex trade, specifically the solicitation of prostitution. Prostitution on the dark web is a growing concern, as it allows individuals to engage in this illegal activity with relative anonymity. “Most of the suspects identified in Operation Stream were matched against records in Europol’s databases, proving that most offenders engaged in child sexual exploitation are repeat offenders and are not unknown to law enforcement authorities.”
- Therefore, based on the above elements, indirectly counts the number of users in an anonymous network.
- The owners ignore all legalization issues that could arise on the buyer’s side, they just ingenuously offer FedEx delivery.
- The system then looks for similarities in a user’s network, which is the circle of people that the user interacts with, and the topics that the user’s network discusses.
- “The perception of prostitution is more positive when it’s less overtly visible, when it uses terms to disguise itself. What’s more, we’ve detected that men accept it more than women.”
- These search engines catalog .onion domains, which are not easily accessible from regular web browsers.
If the current number of users estimated to the above system is high, it can be concluded that there are possible censorship events, otherwise no. There are mechanisms in the TOR that make assumptions that clients make on average ten requests per day. A TOR client, if it is connected to the Internet 24/7, can make approximately fifteen requests per day, but not all clients stay connected to the Internet 24/7, so it takes into consideration average ten requests per client. The total number of directories’ requests that come from users divide by ten and it is found the number of users.
The accident was an act of both desperation and hope—the woman had climbed out of the sixth-floor window to escape a group of men who had been sexually abusing her and holding her captive for two days. Guido Limmer, the deputy head of the Bavarian Criminal Police, told CBS News that a 36-year-old German man was among those arrested. He not only allegedly searched for CSAM on KidFlix but “offered his young son for games,” Limmer said. Europol has shut down one of the largest dark web pedophile networks in the world, prompting dozens of arrests worldwide and threatening that more are to follow. A not-for-profit organization, IEEE is the world’s largest technical professional organization dedicated to advancing technology for the benefit of humanity.© Copyright 2025 IEEE – All rights reserved.
New Risks
When a bitcoin is used in a financial transaction, the transaction is recorded in a public ledger, called the block chain. The information recorded in the block chain is the bitcoin addresses of the sender and recipient. An address does not uniquely identify any particular bitcoin; rather, the address merely identifies a particular transaction 30 . It is a decentralized digital currency that uses anonymous, peer-to-peer transactions 28 .